[ad_1]

Credit score:
metamorworks/shutterstock.com
We’re excited to introduce our fourth visitor creator on this weblog collection, Chike Abuah, PhD scholar in pc science on the College of Vermont, whose analysis expands the state-of-the-art within the topic of this weblog submit: static and dynamic evaluation approaches to automated proofs of differential privateness. – Joseph Close to and David Darais
Beforehand, now we have mentioned some differentially personal algorithms and implementation bugs which might trigger these algorithms to fail to guard privateness in apply. Earlier posts have described two methods of addressing this drawback: automated testing and guide proofs.
On this submit, we look at a 3rd choice: automated proof. Automated proof instruments for differential privateness analyze this system and try and construct a proof that this system satisfies differential privateness.
The testing instruments described within the final submit can be utilized on any program, written in any programming language. Nonetheless, testing-based instruments can solely discover bugs – they’ll by no means show that no bugs exist. The automated proof instruments described on this submit are much less broadly relevant, however can produce a proof of privateness equal to the guide proofs written by privateness consultants.
Automated proof instruments for differential privateness are divided into two classes: static evaluation instruments assemble a proof with out operating this system (like the kind checker in Java); dynamic evaluation instruments assemble a proof whereas operating this system, utilizing a dynamic monitor executed by the unmodified runtime system (e.g. the Python interpreter or Java Digital Machine). The ensuing proof might apply solely to that execution of this system. Determine 1 summarizes these two classes, and lists a number of the instruments which have been developed in every class. We’ll describe particular options of a few of these instruments later within the submit.
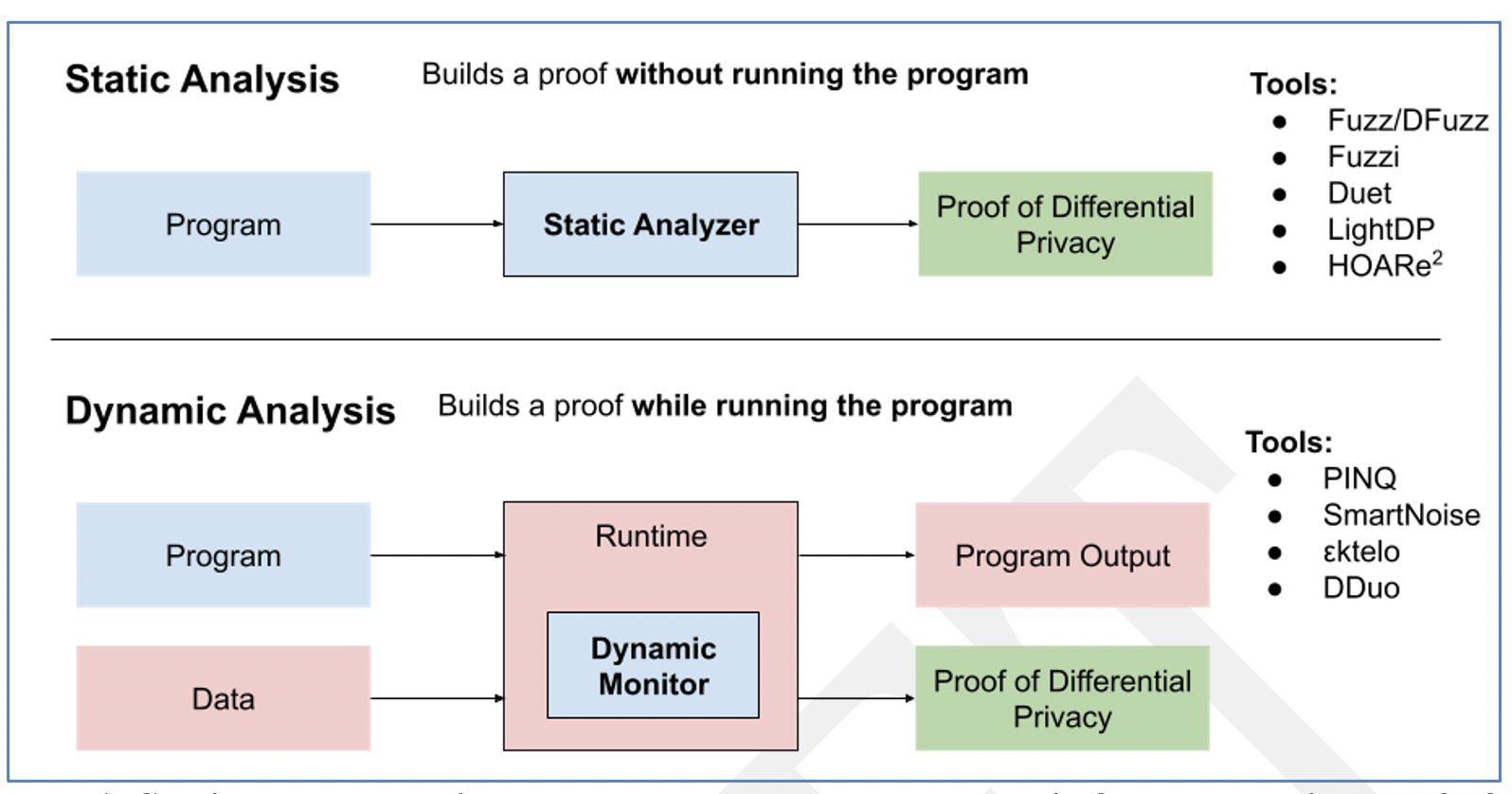
Determine 1. Static and dynamic approaches to program evaluation for automated proof of differential privateness.
Design Necessities for Automated Proof
One of the common strategies for evaluation of differential privateness for an algorithm is to transform a daily algorithm right into a randomized model of the identical algorithm. When developing a proof of privateness, there are three main factors to contemplate:
- Decide the worldwide sensitivity of the algorithm to confidential info
- Add random noise to the output of the algorithm proportional to its sensitivity
- If the algorithm consists of a number of privacy-preserving algorithms, we should additionally think about composition
Thus, automated proof instruments have two principal issues: the willpower of sensitivity for an “atomic” personal algorithm, and the composition of a number of personal algorithms. Ideally, our instruments would accommodate each of those options.
Static Evaluation for Differential Privateness
The Fuzz language design proposes a brand-new programming language and specialised sort system to statically confirm differential privateness of applications mechanically for ε-differential privateness particularly. Fuzz implements a “linear sort system” to trace and analyze variable utilization with the intention to cause about international sensitivity of confidential info. This strategy is much like the side of the Rust sort system which ensures reminiscence security of applications; Rust does this by way of one other type of linear sorts. The linear sorts required for sensitivity evaluation are nonetheless extra refined than these seen in Rust, and presently don’t exist in any mainstream programming language. Nonetheless, the Fuzz strategy remains to be very compelling, and has been prolonged/constructed upon in plenty of subsequent analysis endeavours, equivalent to DFuzz and Duet.
The static strategy typically is enticing as a result of it permits applications to be verified as differentially personal for confidential inputs, with out ever having to run this system on any information. Intuitively, this tells us that when this system truly executes it is not going to introduce any privateness bugs whatever the precise program inputs on that execution. Sustaining an identical data-independent assure within the dynamic evaluation setting is tougher, though doable with sure extra restrictions on this system, equivalent to limitations on conditionals.
A barrier to adoption for Fuzz-like approaches is the shortage of assist for expressing these refined sort methods in mainstream programming languages.
Dynamic Evaluation for Differential Privateness
The PINQ system (code out there right here) is a device for dynamic evaluation of differentially personal applications; it analyzes the privateness properties of this system throughout this system’s execution, and throws an error if privateness could be violated. PINQ is designed for dynamic information evaluation on a relational database preserving differential privateness. It helps a subset of SQL operations equivalent to The place, Choose, GroupBy, and Be a part of. The PINQ code pattern proven under counts searches by distinct customers based mostly on their IP addresses. This program masses in a delicate database as a PINQueryable, permitting entry to the database information by way of a restricted API which tracks the worldwide sensitivity of this system.
var information = new PINQueryable( … … );
var customers = from document in information
the place document.Question == argv[0]
groupby document.IPAddress
Console.WriteLine(argv[0] + “: “ + customers.NoisyCount(0.1));
A number of subsequent analysis initiatives have been based mostly on PINQ, additionally concentrating on a relational database question mannequin. Dynamic enforcement approaches for differential privateness should be rigorously carried out to mitigate potential exploitation of program side-effects and aspect channels. Because of this, operations are often very restricted within the out there programming mannequin.
Extra not too long ago, general-purpose open-source privateness evaluation initiatives equivalent to εktelo, Smartnoise, and Diffprivlib intention to make dynamic privateness enforcement accessible as library utilities in mainstream dynamically typed languages. Different work has tried to make privateness evaluation pervasive all through the programming mannequin of the core of a language equivalent to Python, utilizing strategies much like dynamic taint evaluation, which has traditionally been used to implement different safety properties equivalent to info management circulate (confidentiality, integrity, and so forth.) Automated enforcement of differential privateness in mainstream languages equivalent to Python “by design” has the potential to be helpful and handy, however comes with mandatory drawbacks, equivalent to limitations on the usage of conditionals.
One other particular problem arises within the dynamic setting: sequential composition theorems for differential privateness are designed to have the privateness parameters fastened up-front, or statically, and don’t essentially permit these parameters to be picked adaptively, probably based mostly on the results of prior computations. Nonetheless privateness filters and odometers, developed in latest analysis works, could also be used within the adaptive setting to permit for adaptive parameter choice. Whereas privateness odometers permit the analyst to compute an higher sure on the entire privateness leakage at any level in a sequence of adaptive personal computations, privateness filters permit the analyst to position an higher sure on her desired privateness value for a sequence of adaptive personal computations, and halt the method instantly if the sure is exceeded.
Software program Instruments
Automated proof instruments (for differential privateness, and for different properties of applications) is an energetic space of analysis, and new instruments are developed on a regular basis. As a result of they’re extra simply built-in into current programming languages, dynamic evaluation instruments are typically extra mature and nearer to production-ready. The Smartnoise and Diffprivlib methods, for instance, each present well-maintained open-source frameworks for constructing differentially personal evaluation pipelines with automated proofs of differential privateness based mostly on dynamic evaluation. Guaranteeing that analyses are freed from privateness bugs is a serious benefit of constructing on methods like these. Open-source dynamic evaluation instruments embody:
Static approaches like Fuzz, as described earlier, are rather more tough to combine with current instruments. Nonetheless, as static program evaluation strategies change into extra mature, and as mainstream programming languages acquire extra refined sort methods, static approaches might change into simply as simple to make use of as dynamic ones. Open-source static evaluation instruments embody:
HOARe2 (paper, device)
Many of those instruments can be found within the NIST Privateness Engineering Collaboration Area.
Coming Up Subsequent
The vast majority of the posts on this collection, together with this one, have targeted on technical approaches for attaining differential privateness. In our subsequent submit, we’ll return to the topic of what differential privateness means, what it protects and does not shield, and the all-important query of learn how to set the privateness price range.
This submit is a part of a collection on differential privateness. Be taught extra and browse all of the posts revealed so far on the differential privateness weblog collection web page in NIST’s Privateness Engineering Collaboration Area.
[ad_2]
Source link