[ad_1]

Getty Photos
An unusually superior hacking group has spent nearly two years infecting a variety of routers in North America and Europe with malware that takes full management of linked units working Home windows, macOS, and Linux, researchers reported on Tuesday.
Thus far, researchers from Lumen Applied sciences’ Black Lotus Labs say they’ve recognized not less than 80 targets contaminated by the stealthy malware, infecting routers made by Cisco, Netgear, Asus, and DayTek. Dubbed ZuoRAT, the distant entry Trojan is a part of a broader hacking marketing campaign that has existed since not less than the fourth quarter of 2020 and continues to function.
A excessive stage of sophistication
The invention of custom-built malware written for the MIPS structure and compiled for small workplace and residential workplace routers is critical, notably given its vary of capabilities. Its means to enumerate all units linked to an contaminated router and accumulate the DNS lookups and community site visitors they ship and obtain and stay undetected is the hallmark of a extremely refined menace actor.
“Whereas compromising SOHO routers as an entry vector to achieve entry to an adjoining LAN isn’t a novel method, it has seldom been reported,” Black Lotus Labs researchers wrote. “Equally, reviews of person-in-the-middle type assaults, resembling DNS and HTTP hijacking, are even rarer and a mark of a fancy and focused operation. Using these two strategies congruently demonstrated a excessive stage of sophistication by a menace actor, indicating that this marketing campaign was presumably carried out by a state-sponsored group.”
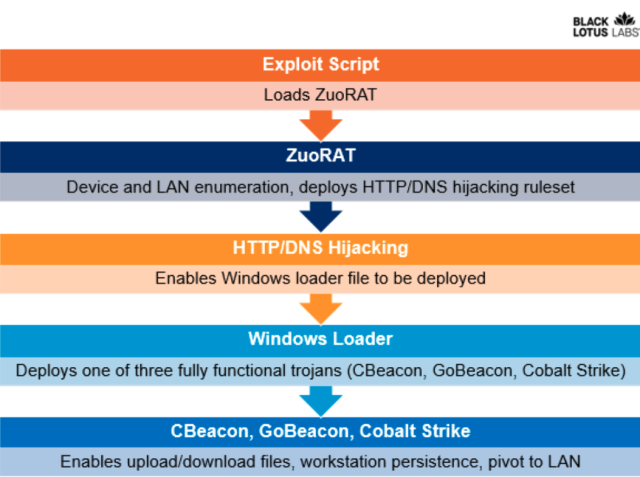
The marketing campaign includes not less than 4 items of malware, three of them written from scratch by the menace actor. The primary piece is the MIPS-based ZuoRAT, which carefully resembles the Mirai Web of Issues malware that achieved record-breaking distributed denial-of-service assaults that crippled some Web providers for days. ZuoRAT usually will get put in by exploiting unpatched vulnerabilities in SOHO units.
As soon as put in, ZuoRAT enumerates the units linked to the contaminated router. The menace actor can then use DNS hijacking and HTTP hijacking to trigger the linked units to put in different malware. Two of these malware items—dubbed CBeacon and GoBeacon—are custom-made, with the primary written for Home windows in C++ and the latter written in Go for cross-compiling on Linux and macOS units. For flexibility, ZuoRAT may infect linked units with the extensively used Cobalt Strike hacking software.
Black Lotus Labs
ZuoRAT can pivot infections to linked units utilizing one in every of two strategies:
- DNS hijacking, which replaces the legitimate IP addresses comparable to a website resembling Google or Fb with a malicious one operated by the attacker.
- HTTP hijacking, by which the malware inserts itself into the connection to generate a 302 error that redirects the person to a special IP deal with.
Deliberately advanced
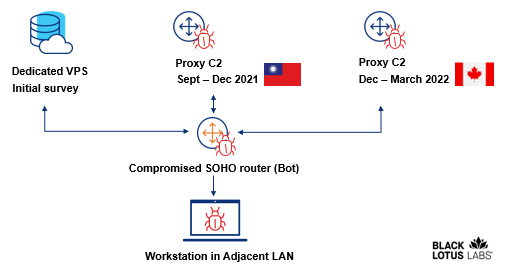
Black Lotus Labs stated the command and management infrastructure used within the marketing campaign is deliberately advanced in an try to hide what’s occurring. One set of infrastructure is used to manage contaminated routers, and one other is reserved for the linked units in the event that they’re later contaminated.
The researchers noticed routers from 23 IP addresses with a persistent connection to a management server that they consider was performing an preliminary survey to find out if the targets have been of curiosity. A subset of these 23 routers later interacted with a Taiwan-based proxy server for 3 months. An extra subset of routers rotated to a Canada-based proxy server to obfuscate the attacker’s infrastructure.
This graphic illustrates the steps listed concerned.
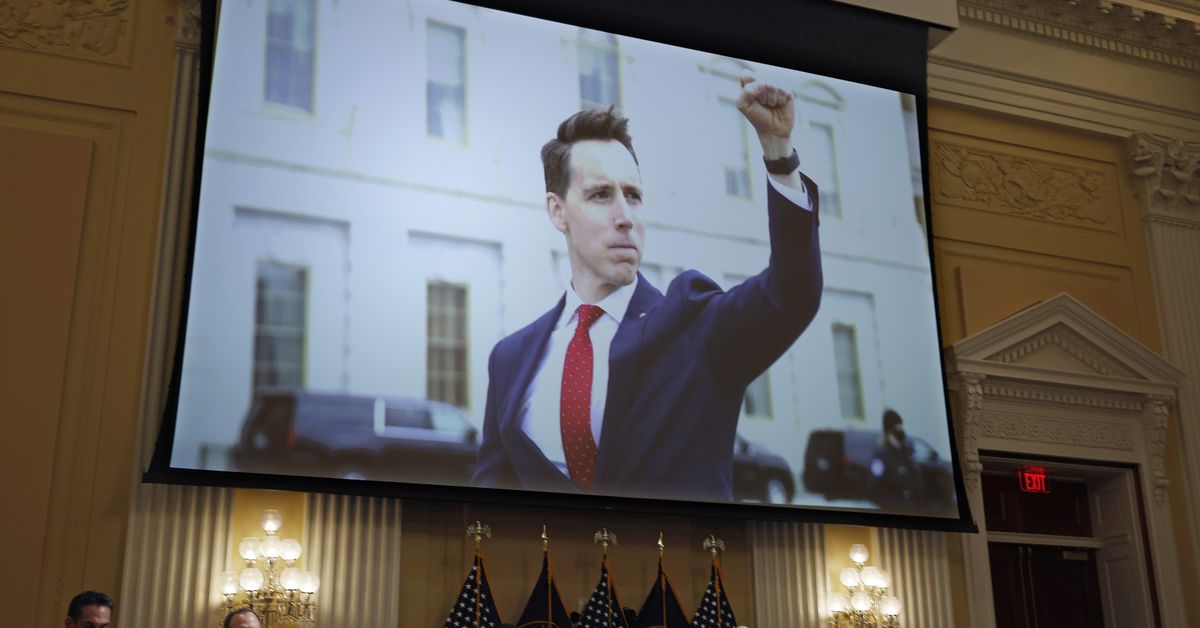
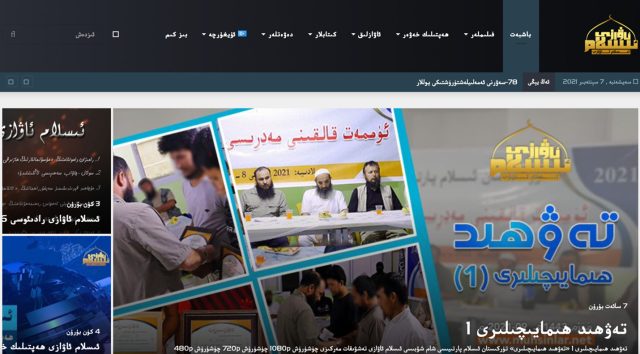
The menace actors additionally disguised the touchdown web page of a management server to appear to be this:
Black Lotus Labs
The researchers wrote:
Black Lotus Labs visibility signifies ZuoRAT and the correlated exercise characterize a extremely focused marketing campaign towards US and Western European organizations that blends in with typical web site visitors via obfuscated, multistage C2 infrastructure, doubtless aligned with a number of phases of the malware an infection. The extent to which the actors take pains to cover the C2 infrastructure can’t be overstated. First, to keep away from suspicion, they handed off the preliminary exploit from a devoted digital personal server (VPS) that hosted benign content material. Subsequent, they leveraged routers as proxy C2s that hid in plain sight via router-to-router communication to additional keep away from detection. And eventually, they rotated proxy routers periodically to keep away from detection.
The invention of this ongoing marketing campaign is crucial one affecting SOHO routers since VPNFilter, the router malware created and deployed by the Russian authorities that was found in 2018. Routers are sometimes ignored, notably within the work-from-home period. Whereas organizations usually have strict necessities for what units are allowed to attach, few mandate patching or different safeguards for the units’ routers.
Like most router malware, ZuoRAT cannot survive a reboot. Merely restarting an contaminated machine will take away the preliminary ZuoRAT exploit, consisting of recordsdata saved in a brief listing. To totally get better, nonetheless, contaminated units ought to be manufacturing unit reset. Sadly, within the occasion linked units have been contaminated with the opposite malware, they cannot be disinfected so simply.
[ad_2]
Source link