[ad_1]
Classen et al.
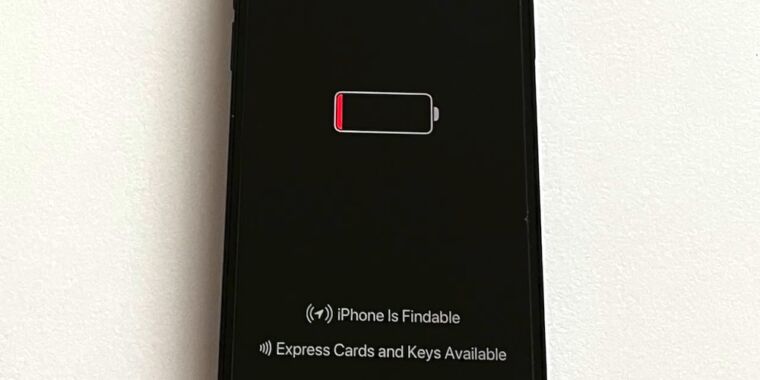
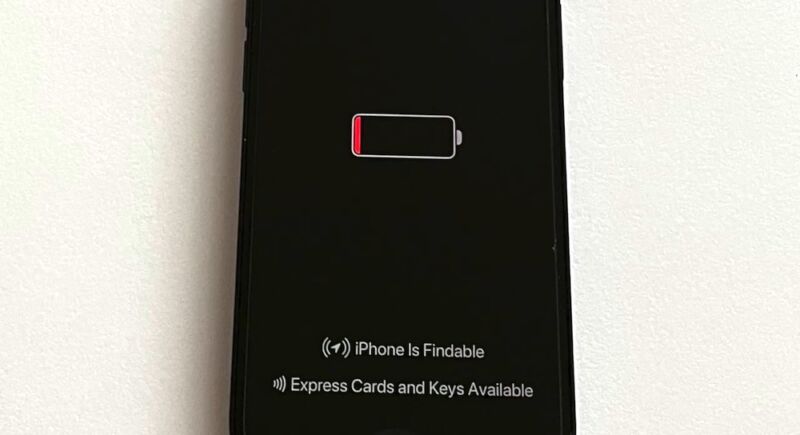
While you flip off an iPhone, it doesn’t absolutely energy down. Chips contained in the machine proceed to run in a low-power mode that makes it attainable to find misplaced or stolen units utilizing the Discover My function or use bank cards and automobile keys after the battery dies. Now researchers have devised a approach to abuse this always-on mechanism to run malware that continues to be lively even when an iPhone seems to be powered down.
It seems that the iPhone’s Bluetooth chip—which is essential to creating options like Discover My work—has no mechanism for digitally signing and even encrypting the firmware it runs. Teachers at Germany’s Technical College of Darmstadt discovered how you can exploit this lack of hardening to run malicious firmware that permits the attacker to trace the telephone’s location or run new options when the machine is turned off.
This video offers a excessive overview of a number of the methods an assault can work.
[Paper Teaser] Evil By no means Sleeps: When Wi-fi Malware Stays On After Turning Off iPhones.
The analysis is the primary—or at the very least among the many first—to review the chance posed by chips working in low-power mode. To not be confused with iOS’s low-power mode for conserving battery life, the low-power mode (LPM) on this analysis permits chips answerable for near-field communication, extremely wideband, and Bluetooth to run in a particular mode that may stay on for twenty-four hours after a tool is turned off.
“The present LPM implementation on Apple iPhones is opaque and provides new threats,” the researchers wrote in a paper revealed final week. “Since LPM help relies on the iPhone’s {hardware}, it can’t be eliminated with system updates. Thus, it has a long-lasting impact on the general iOS safety mannequin. To the very best of our data, we’re the primary who seemed into undocumented LPM options launched in iOS 15 and uncover numerous points.”
They added: “Design of LPM options appears to be largely pushed by performance, with out contemplating threats outdoors of the meant functions. Discover My after energy off turns shutdown iPhones into monitoring units by design, and the implementation inside the Bluetooth firmware isn’t secured in opposition to manipulation.”
The findings have restricted real-world worth since infections required a jailbroken iPhone, which in itself is a troublesome process, significantly in an adversarial setting. Nonetheless, focusing on the always-on function in iOS might show useful in post-exploit situations by malware corresponding to Pegasus, the subtle smartphone exploit instrument from Israel-based NSO Group, which governments worldwide routinely make use of to spy on adversaries.
It could even be attainable to contaminate the chips within the occasion hackers uncover safety flaws which are prone to over-the-air exploits just like this one which labored in opposition to Android units.
Moreover permitting malware to run whereas the iPhone is turned off, exploits focusing on LPM might additionally enable malware to function with far more stealth since LPM permits firmware to preserve battery energy. And naturally, firmware infections are already extraordinarily troublesome to detect due to the numerous experience and costly gear required to take action.
The researchers stated Apple engineers reviewed their paper earlier than it was revealed, however firm representatives by no means supplied any suggestions on its contents. Apple representatives didn’t reply to an electronic mail in search of remark for this story.
In the end, Discover My and different options enabled by LPM assist present added safety as a result of they permit customers to find misplaced or stolen units and lock or unlock automobile doorways even when batteries are depleted. However the analysis exposes a double-edged sword that, till now, has gone largely unnoticed.
“{Hardware} and software program assaults just like those described, have been confirmed sensible in a real-world setting, so the subjects coated on this paper are well timed and sensible,” John Loucaides, senior vp of technique at firmware safety agency Eclypsium. “That is typical for each machine. Producers are including options on a regular basis and with each new function comes a brand new assault floor.”
[ad_2]
Source link