[ad_1]
In case you’ve ever learn a privateness coverage, you might have seen a bit that claims one thing about how your information can be shared with regulation enforcement, which implies if the police demand it and have the mandatory paperwork, they’ll probably get it. However perhaps, like most American adults, you don’t learn privateness insurance policies very fastidiously if in any respect. In that case, you is likely to be stunned to learn the way a lot of your information is within the fingers of third events, how a lot entry regulation enforcement has to it, the way it is likely to be used in opposition to you, or what your rights are — if any — to stop it.
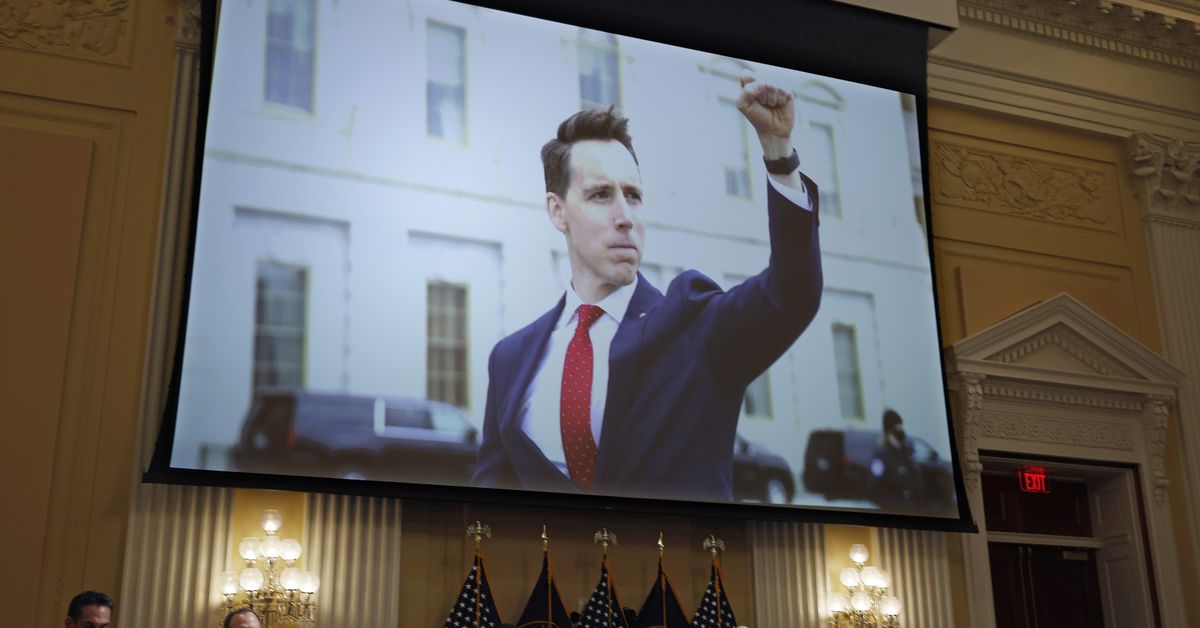
Lots of the Capitol insurrectionists is likely to be discovering this now, as circumstances in opposition to them are constructed with proof taken from web companies like Fb and Google. Whereas they left a path of digital proof for investigators (and web detectives) to comply with, not all of that information was publicly obtainable. In case you learn by way of circumstances of individuals charged with crimes regarding the occasions in Washington on January 6, you’ll discover the FBI additionally obtained inside data from numerous social media platforms and cell phone carriers.
However you don’t must be an alleged insurrectionist for regulation enforcement to get information about you from one other firm. In actual fact, you don’t must be suspected of a criminal offense in any respect. The police are more and more utilizing ways like reverse search warrants to seize the information of many individuals within the hope of discovering their suspect amongst them. You may get swept up in a single simply since you had been within the unsuitable place on the unsuitable time or seemed up the unsuitable search time period. And also you may by no means know that you just received caught within the dragnet.
“Investigators are going to those suppliers with out a suspect and asking for a broad set of knowledge that’s not focused with a purpose to mainly establish suspects that they didn’t already keep in mind,” Jennifer Granick, surveillance and cybersecurity counsel for the ACLU’s speech, privateness, and expertise undertaking, informed Recode. “These extra mass surveillance strategies are more and more frequent.”
Mainly, if an organization collects and shops your information, then the police can in all probability get their fingers on it. And in the case of your digital life, there’s a whole lot of your information held by third events on the market to acquire. Right here’s how they get it.
How regulation enforcement buys your information, no warrant wanted
The excellent news is there are some privateness legal guidelines that govern if and the way the federal government can get your information: The Digital Communications Privateness Act (ECPA), first enacted in 1986, established these guidelines.
However the regulation is a number of a long time outdated. Whereas it has been up to date since 1986, a lot of its tenets don’t actually mirror how we use the web immediately, or how a lot of our information stays within the fingers of the businesses that present these companies to us.
Meaning there are grey areas and loopholes, and for some issues, the federal government doesn’t must undergo any authorized processes in any respect. Regulation enforcement can and does buy location information from information brokers, as an example. And whereas location information corporations declare that their information has been de-identified, specialists say it’s usually attainable to re-identify people.
“The notion is that if it’s obtainable on the market, then it’s okay,” mentioned Kurt Opsahl, deputy government director and normal counsel for the Digital Frontier Basis (EFF). “After all, one of many issues is that a whole lot of these information brokers are getting info with out going by way of the consent course of that you may want.”
And it’s not simply location information. Facial recognition firm Clearview AI’s complete enterprise mannequin is to promote regulation enforcement businesses entry to its facial recognition database, a lot of which was culled from publicly obtainable images Clearview scraped from the web. Until you reside in a metropolis or state that has outlawed facial recognition, it’s presently authorized for the police to pay in your face information, no matter how flawed the expertise behind it might be.
This might change if one thing just like the Fourth Modification Is Not for Sale Act, which bans regulation enforcement from buying commercially obtainable information, had been to turn out to be regulation. However for now, the loophole is open.
“One of many challenges with any expertise regulation is expertise evolves quicker than the regulation,” Opsahl mentioned. “It’s at all times a problem to use these legal guidelines to a contemporary setting, however [ECPA] nonetheless has, all these many a long time later, supplied a stable privateness safety. There positively may very well be enhancements, but it surely’s nonetheless doing good work immediately.”
What regulation enforcement can get by way of the courts
In case you’re suspected of a criminal offense and police are in search of proof in your digital life, then ECPA says they will need to have a subpoena, courtroom order, or warrant earlier than an organization is allowed to offer the information they’re requesting. That’s to say, the corporate can’t simply hand it over voluntarily. There are just a few exceptions — as an example, if there’s motive to consider there’s imminent hazard or a criminal offense is in progress. However within the case of prison investigations, these exceptions don’t apply.
Broadly, the authorized course of that investigators have to make use of is determined by what information they’re in search of:
- Subpoena: This provides investigators what’s generally known as subscriber info, akin to your identify, tackle, size of service (how lengthy you’ve had your Fb profile, for instance), log info (while you’ve made cellphone calls or logged into and out of your Fb account), and bank card info.
- Court docket order, or “D” order: The D refers to 18 US Code § 2703(d), which says a courtroom might order web service suppliers to offer regulation enforcement any data in regards to the subscriber apart from the content material of their communications. So that would embody who emailed you and when, however not the contents of the particular e mail.
- Search warrant: This provides regulation enforcement entry to content material itself, particularly saved content material, which incorporates emails, images, movies, posts, direct messages, and placement info. Whereas the ECPA says that emails saved for over 180 days may be obtained with only a subpoena, that rule dates again to earlier than folks routinely stored their emails on one other firm’s server (how far again does your Gmail inbox go?) or used it as a backup. At this level, a number of courts have dominated {that a} warrant is important for e mail content material no matter how outdated the emails are, and repair suppliers usually demand a warrant earlier than they’ll agree at hand them over.
If you wish to get an thought of how usually the federal government requests information from these corporations, a few of them do launch transparency experiences that give fundamental particulars about what number of requests they get, what kind, and what number of of these requests they fulfill. In addition they present how a lot these requests have elevated over time. Right here’s Fb’s transparency report, right here’s Google’s, and right here’s Apple’s. The EFF additionally put out a information in 2017 exhibiting how a number of tech corporations reply to authorities requests.
You don’t must be a suspect or concerned in a criminal offense for regulation enforcement to get your information
So, let’s say you’ve determined that you’ll by no means commit a criminal offense so regulation enforcement acquiring your information won’t ever be a difficulty for you. You’re unsuitable.
As talked about above, your information may very well be included in a purchase order from an information dealer. Or it might be scooped up in a digital dragnet, often known as a reverse search warrant, the place police request information about a big group of individuals within the hope of discovering their suspect inside them.
“These are novel strategies to find issues that by no means might have been found prior to now, and which have the capability to rope in harmless folks,” Granick, of the ACLU, mentioned.
Two examples of this: the place you went and what you looked for. In a geofence warrant, regulation enforcement will get details about all of the gadgets that had been in a sure space at a sure time — say, the place a criminal offense occurred — then narrows them down and will get account info for the gadget(s) they assume belong to their suspect(s). For key phrase warrants, police might ask a browser for all of the IP addresses that looked for a sure time period associated to their case after which establish a attainable suspect from that group.
These conditions nonetheless symbolize a authorized grey space. Whereas some judges have known as them a Fourth Modification violation and refused the federal government’s requests for warrants, others have allowed them. And we’ve seen a minimum of one occasion the place reverse search warrants have led to the arrest of an harmless individual.
You is probably not informed for years that your information was obtained — when you’re informed in any respect
One other troubling facet to that is that, relying on what’s being requested and why, you could by no means know if police requested your information from an organization or if that firm gave it to them. In case you’re charged with a criminal offense and that information is used as proof in opposition to you, then you definitely’ll know. But when your information is obtained by way of buy from an information dealer or as a part of a bulk request, you won’t. If an organization tells you that regulation enforcement desires your information and provides you advance discover, then you’ll be able to attempt to struggle their request your self. However investigators can get gag orders that forestall corporations from telling customers something, at which level you’re left to hope that the corporate fights for you.
In accordance with their transparency experiences, Google, Apple, and Fb do seem to struggle or push again generally — for instance, in the event that they assume a request is overly broad or burdensome — so not each request is profitable. However that’s them. It’s not essentially true of everybody.
“Not each supplier is a Google or a Fb that has a deep-bench authorized division with severe experience in federal surveillance regulation,” Granick mentioned “Some suppliers, we don’t know what they do. Possibly they don’t do something. That’s an actual situation.”
The vast majority of authorities requests even to the largest corporations on this planet consequence within the disclosure of a minimum of some person information, and we’ve seen circumstances the place somebody’s information was given to the federal government and that individual didn’t know for years. As an illustration, the Division of Justice obtained Democratic Reps. Adam Schiff’s and Eric Swalwell’s subscriber data (and that of their members of the family) from Apple by way of a grand jury subpoena. This occurred in 2017 and 2018, however the Congress members solely discovered about it in June 2021, when the gag order expired.
In case your info is swept up in one thing like a reverse search warrant however you’re by no means recognized as a suspect or charged, you could by no means find out about it in any respect if the corporate that supplied it doesn’t inform you. Opsahl, of the EFF, mentioned that many of the main tech corporations publish transparency experiences and it’s thought of an business greatest observe to take action. That doesn’t imply all of them comply with it, nor have they got to.
How one can forestall this
Relating to your information held by third events, you don’t have a lot management or say over if and what they’ll disclose. You’re counting on legal guidelines written earlier than the trendy web existed, a choose’s interpretation of them (assuming it goes earlier than a choose, which subpoenas might not), and the businesses which have your information to struggle them. In case you’re notified a couple of pending order, you may be capable to struggle it your self. That’s no assure you’ll win.
One of the simplest ways to guard your information is to make use of companies that don’t get it within the first place. Privateness considerations, together with the power to speak free from authorities surveillance, have made encrypted messaging apps like Sign and personal browsers like DuckDuckGo well-liked lately. They decrease the information they acquire from customers, which implies they don’t have a lot to offer if investigators attempt to acquire it. You may as well ask companies to delete your information from their servers or not add it to them within the first place (assuming these are choices). The FBI can’t get a lot from Apple’s iCloud when you haven’t uploaded something to it.
At that time, investigators must attempt to get the information they need out of your gadget … which is a complete different can of authorized worms.
[ad_2]
Source link