[ad_1]

Getty Pictures
For greater than a decade, we’ve been promised {that a} world with out passwords is simply across the nook, and but 12 months after 12 months, this safety nirvana proves out of attain. Now, for the primary time, a workable type of passwordless authentication is about to turn into obtainable to the lots within the type of a regular adopted by Apple, Google, and Microsoft that permits for cross-platform and cross-service passkeys.
Password-killing schemes pushed up to now suffered from a number of issues. A key shortcoming was the shortage of a viable restoration mechanism when somebody misplaced management of cellphone numbers or bodily tokens and telephones tied to an account. One other limitation was that almost all options finally did not be, in reality, actually passwordless. As a substitute, they gave customers choices to log in with a face scan or fingerprint, however these methods finally fell again on a password, and that meant that phishing, password reuse, and forgotten passcodes—all the explanations we hated passwords to start with—didn’t go away.
A brand new method
What’s totally different this time is that Apple, Google, and Microsoft all appear to be on board with the identical well-defined answer. Not solely that, however the answer is simpler than ever for customers, and it is more cost effective for large companies like Github and Fb to roll out. It has additionally been painstakingly devised and peer-reviewed by consultants in authentication and safety.
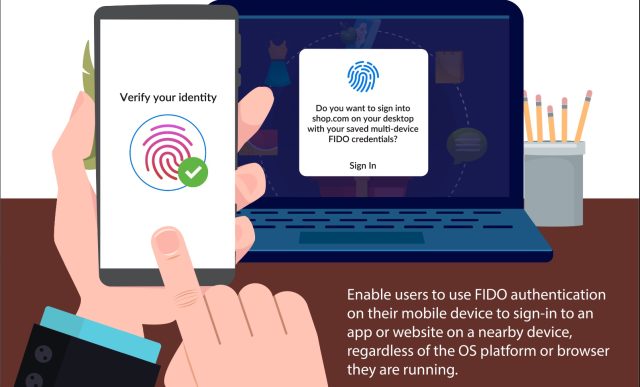
FIDO Alliance
The present multifactor authentication (MFA) strategies have made essential strides over the previous 5 years. Google, as an illustration, permits me to obtain an iOS or Android app that I take advantage of as a second issue when logging in to my Google account from a brand new system. Based mostly on CTAP—brief for shopper to authenticator protocol—this technique makes use of Bluetooth to make sure that the cellphone is in proximity to the brand new system and that the brand new system is, in reality, related to Google and never a website masquerading as Google. Which means it’s unphishable. The usual ensures that the cryptographic secret saved on the cellphone can’t be extracted.
Google additionally supplies an Superior Safety Program that requires bodily keys within the type of standalone dongles or end-user telephones to authenticate logins from new gadgets.
The large limitation proper now’s that MFA and passwordless authentication get rolled out in another way—if in any respect—by every service supplier. Some suppliers, like most banks and monetary companies, nonetheless ship one-time passwords by SMS or e mail. Recognizing that these aren’t safe means for transporting security-sensitive secrets and techniques, many companies have moved on to a way often known as TOTP—brief for time-based one-time password—to permit the addition of a second issue, which successfully augments the password with the “one thing I’ve” issue.
Bodily safety keys, TOTPs, and to a lesser extent two-factor authentication by SMS and e mail characterize an essential step ahead, however there stay three key limitations. First, TOTPs generated by authenticator apps and despatched by textual content or e mail are phishable, the identical method common passwords are. Second, every service has its personal closed MFA platform. That implies that even when utilizing unphishable types of MFA—similar to standalone bodily keys or phone-based keys—a consumer wants a separate key for Google, Microsoft, and each different Web property. To make issues worse, every OS platform has differing mechanisms for implementing MFA.
These issues give option to a 3rd one: the sheer unusability for many finish customers and the nontrivial value and complexity every service faces when making an attempt to supply MFA.
[ad_2]
Source link