[ad_1]
Getty Pictures
From the what-could-possibly-go-wrong information comes this: Individuals hawking password-cracking software program are concentrating on the {hardware} utilized in industrial-control amenities with malicious code that makes their programs a part of a botnet, a researcher reported.
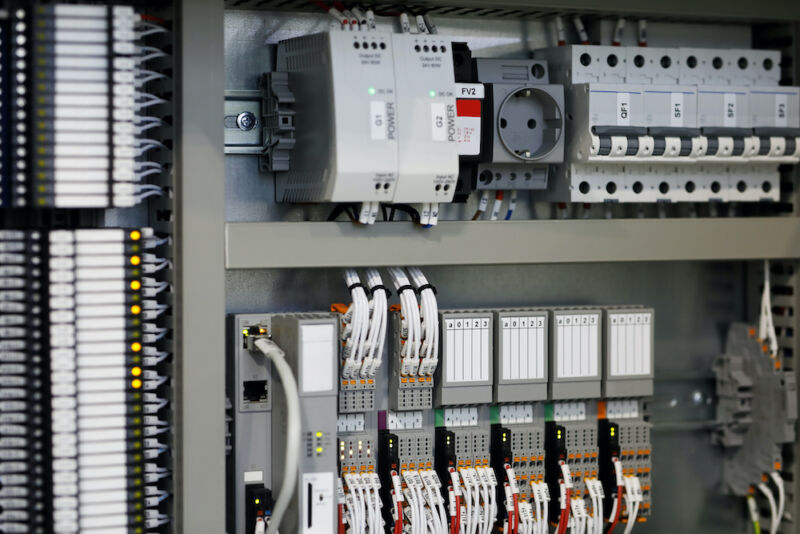
Misplaced passwords occur in lots of organizations. A programmable logic controller—used to automate processes inside factories, electrical vegetation, and different industrial settings, for instance, could also be arrange and largely forgotten over the next years. When a alternative engineer later identifies an issue affecting the PLC, they might uncover the now long-gone unique engineer by no means left the passcode behind earlier than departing the corporate.
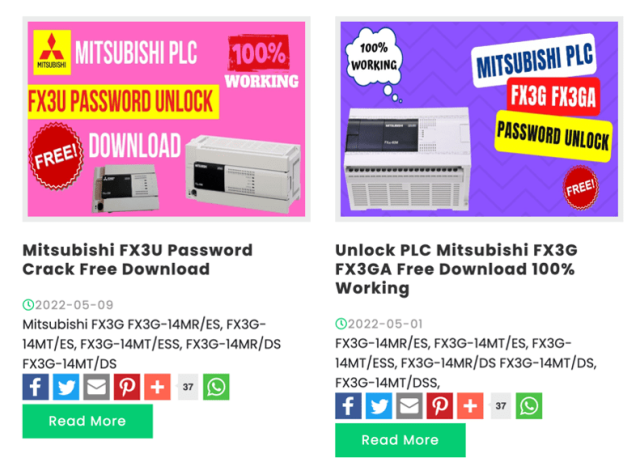
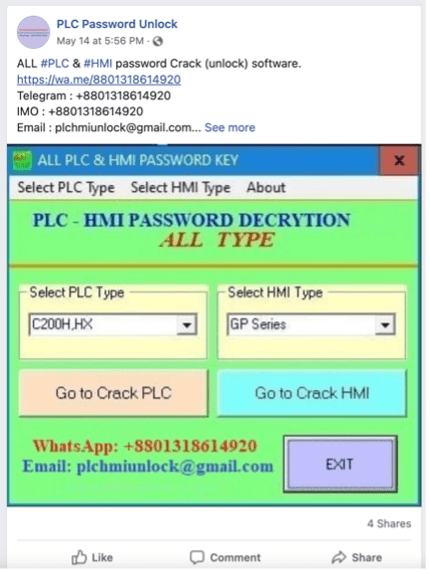
In response to a weblog put up from safety agency Dragos, a whole ecosystem of malware makes an attempt to capitalize on eventualities like this one inside industrial amenities. On-line commercials like these under promote password crackers for PLCs and human-machine interfaces, that are the workhorses inside these environments.
Dragos
Dragos
When your industrial system is a part of a botnet
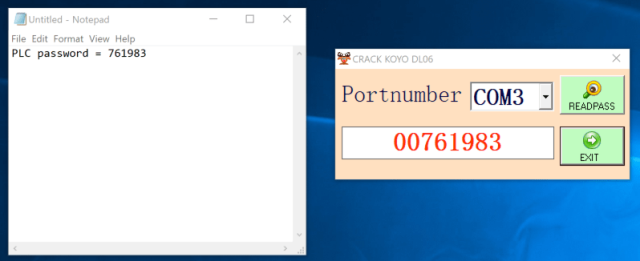
Dragos—which helps corporations safe industrial management programs in opposition to ransomware, state-sponsored hackers, and potential saboteurs—just lately carried out a routine vulnerability evaluation and located software program marketed as password cracker for the DirectLogic 06, a PLC offered by Automation Direct. The software program recovered the password, however not by way of the traditional methodology of cracking the cryptographic hash. As a substitute, the software program exploited a zero-day vulnerability in Computerized Direct PLCs that uncovered the passcode.
Dragos
“Earlier analysis concentrating on DirectLogic PLCs has resulted in profitable cracking methods,” Dragos researcher Sam Hanson wrote. “Nonetheless, Dragos discovered that this exploit doesn’t crack a scrambled model of the password as traditionally seen in fashionable exploitation frameworks. As a substitute, a selected byte sequence is shipped by the malware dropper to a COM port.”
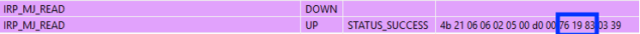
Dragos
The vulnerability, and a associated one additionally discovered by Hanson, have now been patched and are tracked as CVE-2022-2033 and CVE-2022-2004. The latter vulnerability can get well passwords and ship them to a distant hacker, bringing the severity ranking to 7.5 out of a doable 10.
Moreover recovering the password, the software program Hanson analyzed additionally put in malware often called Sality. It made the contaminated system a part of a botnet and monitored the clipboard of the contaminated workstation each half second for any information associated to cryptocurrency pockets addresses.
“If seen, the hijacker replaces the handle with one owned by the menace actor,” Hanson mentioned. “This in-real-time hijacking is an efficient approach to steal cryptocurrency from customers eager to switch funds and will increase our confidence that the adversary is financially motivated.”
Hanson went on to say that he has discovered password crackers marketed on-line for a variety of commercial software program offered by different firms. They embody:
| Vendor and Asset | System Sort |
| Automation Direct DirectLogic 06 | PLC |
| Omron CP1H | PLC |
| Omron C200HX | PLC |
| Omron C200H | PLC |
| Omron CPM2* | PLC |
| Omron CPM1A | PLC |
| Omron CQM1H | PLC |
| Siemens S7-200 | PLC |
| Siemens S7-200 | Venture File (*.mwp) |
| Siemens LOGO! 0AB6 | PLC |
| ABB Codesys | Venture File (*.professional) |
| Delta Automation DVP, ES, EX, SS2, EC Collection | PLC |
| Fuji Electrical POD UG | HMI |
| Fuji Electrical Hakko | HMI |
| Mitsubishi Electrical FX Collection (3U and 3G) | PLC |
| Mitsubishi Electrical Q02 Collection | PLC |
| Mitsubishi Electrical GT 1020 Collection | HMI |
| Mitsubishi Electrical GOT F930 | HMI |
| Mitsubishi Electrical GOT F940 | HMI |
| Mitsubishi Electrical GOT 1055 | HMI |
| Professional-Face GP Professional-Face | HMI |
| Professional-Face GP | Venture File (*.prw) |
| Vigor VB | PLC |
| Vigor VH | PLC |
| Weintek | HMI |
| Allen Bradley MicroLogix 1000 | PLC |
| Panasonic NAIS F P0 | PLC |
| Fatek FBe and FBs Collection | PLC |
| IDEC Company HG2S-FF | HMI |
| LG K80S | PLC |
| LG K120S | PLC |
Dragos examined solely the malware concentrating on the DirectLogic gadgets, however a rudimentary evaluation of some samples indicated additionally they contained malware.
“Basically, it seems there’s an ecosystem for any such software program,” Hanson mentioned. “A number of web sites and a number of social media accounts exist all touting their password ‘crackers.’”
The account is regarding as a result of it illustrates the menace posed to many industrial management settings. The criminals behind the malware Dragos analyzed had been after cash, however there’s no cause extra malicious hackers out to sabotage a dam, energy plant, or comparable facility couldn’t carry out an identical intrusion with way more extreme penalties.
[ad_2]
Source link