[ad_1]

NIST has a historical past of collaboration between its applications, which helps maximize mission impacts and practicality to business. One nice instance is between NIST’s Nationwide Cybersecurity Middle of Excellence (NCCoE) and the Cybersecurity for the Web of Issues (IoT) Program. Latest mission studies from the NCCoE embody mappings of related IoT gadget cybersecurity capabilities and nontechnical supporting capabilities; these three mappings align NIST’s IoT cybersecurity steerage with real-world implementation approaches:
- Securing Telehealth Distant Affected person Monitoring Ecosystem
- Securing Distributed Vitality Sources
- Defending Info and System Integrity in Industrial Management System Environments
Why did we create these mappings, and the way can each prospects and suppliers of IoT gadgets profit from them? Let’s take a more in-depth look.
The background
The NCCoE is a collaborative hub the place organizations throughout industries, authorities companies, and educational establishments work with NIST’s specialists to handle companies’ most urgent cybersecurity challenges. By these collaborations, the NCCoE develops modular, cost-effective, and simply adaptable instance cybersecurity options—making use of requirements, greatest practices, and commercially out there know-how. Organizations can then undertake and combine these modular cybersecurity options into their companies with out disrupting day-to-day operations.
NIST’s Cybersecurity for IoT Program helps the event of requirements, steerage, and associated instruments to enhance the cybersecurity of related gadgets and the environments by which they’re deployed. To combine IoT cybersecurity steerage into real-world eventualities, the IoT crew has been working carefully with the NCCoE. For this collaboration, the IoT crew recognized NCCoE tasks that incorporate IoT gadgets (and subsequently created IoT-specific cybersecurity steerage for these real-world eventualities). This IoT-specific steerage will be leveraged by organizations seeking to implement NCCoE’s modular cybersecurity options[1]. However there’s one other potential beneficiary of the IoT-specific steerage: the producers of the IoT gadgets.
What IoT-specific steerage was created for these NCCoE tasks?
NIST’s Cybersecurity for IoT Program has outlined a catalog of IoT cybersecurity capabilities:
- Machine cybersecurity capabilities are cybersecurity options or capabilities that IoT gadgets present by means of their very own technical means.
- Nontechnical supporting capabilities are actions {that a} producer or third-party group performs in help of the cybersecurity of an IoT gadget.
Machine cybersecurity capabilities embody options like entry management and knowledge encryption. Examples of nontechnical supporting capabilities embody offering details about software program updates, directions for configuration settings, and provide chain info. Used collectively, these capabilities can assist mitigate cybersecurity dangers associated to using IoT gadgets whereas aiding prospects in reaching their objectives. A subset of the capabilities within the full catalog was used to outline a baseline set of cybersecurity capabilities (see NISTIR 8259A and NISTIR 8259B) that producers ought to contemplate integrating into their IoT gadgets and that customers ought to contemplate enabling/configuring in these gadgets.
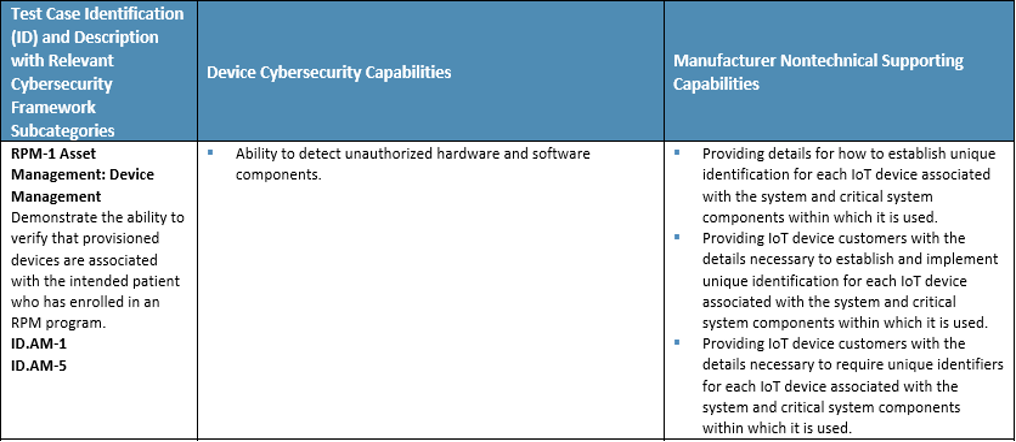
Every NCCoE mission identifies analysis standards–methods to evaluate how nicely the mission’s reference design addresses the safety necessities that it was supposed to help. Primarily, the IoT-specific steerage for the NCCoE tasks maps each technical capabilities and nontechnical supporting capabilities to the mission’s recognized analysis standards, linking the capabilities to a real-world resolution. Mainly, the mappings reply the query: what are the IoT technical and nontechnical capabilities that may greatest assist organizations securely implement the NCCoE mission resolution of their environments?
How have been the mappings created?
The IoT crew beforehand mapped every of the gadget cybersecurity capabilities and nontechnical supporting capabilities to Subcategory outcomes from the NIST Cybersecurity Framework (see SP 800-213A Appendix C). Equally, every NCCoE mission lists key Cybersecurity Framework Subcategory outcomes which are related to the general mission and to the mission’s analysis standards. Utilizing this info, the IoT crew recognized IoT gadget cybersecurity capabilities and nontechnical supporting capabilities that align with every of the NCCoE mission’s objectives and analysis standards.
What do the mappings appear to be?
Beneath is an instance mapping from one of many tasks: Securing Telehealth Distant Affected person Monitoring Ecosystem, exhibiting each gadget cybersecurity capabilities and producer nontechnical supporting capabilities related to one of many mission’s analysis standards.
Who can profit from these mappings?
For organizations implementing the NCCoE mission’s instance resolution of their setting, the mapping demonstrates technical capabilities that these organizations ought to search for in IoT gadgets. The mapping additionally lists nontechnical capabilities that they could search for from a producer or third celebration supporting the IoT gadget. Choosing gadgets and producers/third events that present these capabilities can facilitate the safe deployment of IoT gadgets into the group’s setting.
The mappings can even present advantages for IoT gadget producers (they illustrate the technical and nontechnical capabilities that organizations will likely be searching for in IoT gadgets and from producers). Producers might profit from incorporating these technical capabilities into their gadgets and in growing nontechnical capabilities to supply providers for his or her prospects. Producers offering these desired nontechnical capabilities for his or her prospects and designing IoT gadgets (which give desired technical capabilities) will reveal cybersecurity due diligence; in addition they might achieve a aggressive edge.
Transferring ahead, the Cybersecurity for IoT Program will proceed collaborating with the NCCoE to develop IoT-specific steerage for tasks containing IoT gadgets. As all the time, NIST welcomes your suggestions. Contact us at IoTSecurity [at] NIST.gov.
[ad_2]
Source link