[ad_1]

Credit score:
metamorworks/shutterstock.com
In earlier posts we mentioned many features of differential privateness: what it’s, what it’s helpful for, and the way it’s utilized to information evaluation issues. All of these concepts could be utilized when you get your palms on a complete dataset. What if the info you have an interest in extracting insights from belongs to mutually distrusting organizations? For instance, say you run a pumpkin spice latte stand and are questioning in case your pumpkin spice provider is overcharging you in comparison with the industry-wide common. You’re prepared to take part in a examine that computes this common, however not snug giving your uncooked expense information on to a 3rd occasion. Remarkably, computing this common with out sharing any uncooked information is feasible utilizing superior cryptographic strategies, and these strategies can be utilized along with differential privateness to allow information sharing whereas additionally defending privateness. To assist us perceive how these strategies work, we’re delighted to introduce Luís Brandão and René Peralta, who’re with the Privateness Enhancing Cryptography (PEC) undertaking at NIST.
DISCLAIMER: Opinions expressed listed below are by the authors and may to not be construed as official NIST views. Brandão is at NIST as a International Visitor Researcher, Contractor from Strativia. Any point out of business merchandise or reference to industrial organizations is for data solely; it doesn’t suggest advice or endorsement by NIST, nor does it suggest that the merchandise/organizations talked about are essentially one of the best obtainable for the aim.
Joseph Close to and David Darais
On this publish, we illustrate how varied strategies from privacy-enhancing cryptography, coupled with differential privateness, are helpful to guard information privateness whereas enabling information utility. Of notable curiosity is the setting the place there are a number of sources of related information, every having privateness constraints about information sharing. Privateness-enhancing cryptography is of course suited to resolve challenges in multi-party and interactive eventualities, avoiding the sharing of information throughout events. Its mixed use with differential privateness broadens the set of issues that may be dealt with in a privateness defending method. On this publish, we contemplate a use case associated to non-public medical information, however the concepts can simply switch to myriad different settings.
Defending information privateness throughout a number of datasets
Alice is the info steward at hospital HA, liable for a database of affected person medical data. Equally, Bob is the info steward at one other hospital HB. Alice and Bob study of Rya’s ongoing research about correlations between sufferers’ age and analysis. Alice and Bob wish to assist Rya, because the analysis may present helpful insights to derive higher medical practices. Nonetheless, there are privateness restrictions that forestall Alice and Bob from sharing their databases.
Suppose Rya is desirous about studying the variety of sufferers identified with a situation X, by age-range. Differential privateness permits Rya to acquire an approximate outcome from every of the 2 hospitals, every tweaked by a noise addition with a purpose to shield privateness. Nonetheless, the restriction to 2 separate outcomes has shortcomings: (1) when combining the 2 outcomes, Rya is unable to make corrections which may be required due to doable duplicate entries; (2) the pair of particular person replies leaks details about hospital variations, which is unrelated to Rya’s aim.
In distinction to the above situation, privacy-enhancing cryptography (PEC) allows Rya to work together with Alice and Bob to acquire a mixed response that’s corrected with respect to duplicate entries. That is accomplished with out Alice and Bob sharing information between themselves, and with out Rya studying something past the meant output. PEC could be mixed with differential privateness strategies to offer one of the best tradeoff between privateness and accuracy. Desk 1 illustrates how errors could also be launched when not utilizing PEC. The error is within the sum of two correlated counts, which overestimates the true rely within the union of two units. These errors (with charges above 25 % within the instance) can considerably hinder the utility of the outcomes.
Desk 1: Measure (N) of the variety of sufferers with analysis X
|
Age vary |
With out differential privateness |
With differential privateness |
||||||||
|
Precise counts |
Error fee r |
Differentially non-public counts |
Error fee r |
|||||||
|
A |
B |
∪AB |
If N=A+B (no PEC) |
If N=∪AB (with PEC) |
A |
B |
∪AB’ |
If N=A’+B’ (no PEC) |
If N=∪AB’ (with PEC) |
|
|
0–30 |
8 |
11 |
15 |
26.7 % |
0 % |
9.2 |
10.1 |
16.5 |
28.7 % |
10 % |
|
31–60 |
123 |
85 |
172 |
20.9 % |
0 % |
119.5 |
87.2 |
168.3 |
20.2 % |
2.2 % |
|
61–120 |
428 |
632 |
660 |
60.9 % |
0 % |
433.7 |
633.1 |
656.8 |
61.6 % |
0.5 % |
Legend: A (counts at hospital HA); B (counts at hospital HB); ∪AB (counts on the union of hospitals HA and HB); A’, B’, ∪AB’ (differentially non-public variations of A, B, ∪AB); r = N/∪AB − 1.
What’s protected to compute? As mentioned in earlier posts, differential privateness strategies add noise to the precise results of a question, to restrict privateness loss whereas nonetheless enabling a helpful reply to related queries to a database. From a privateness perspective, the approximate result’s “safer” than an correct reply. PEC strategies obtain one thing totally different: they circumscribe the disclosure to solely the desired remaining output, even when the supply inputs are distributed throughout varied events. Such disclosure is “safer” (with respect to privateness and accuracy) than replies that would come with remoted solutions from every separate supply. That is achieved with cryptographic strategies that emulate an interplay that may be mediated by a (non-existing) trusted third occasion. The PEC and the differential privateness paradigms could be composed to allow higher privateness safety, particularly in eventualities the place delicate information ought to stay confidential in every particular person unique supply. Differential privateness adjusts the question outcome into a loud approximation of the correct reply, which PEC can compute with out exfiltrating further data to any occasion.
Privateness-enhancing cryptography strategies
The following paragraphs contemplate 5 privacy-enhancing cryptography strategies: secure multiparty computation (SMPC), private set intersection (PSI), private information retrieval (PIR), zero-okaynowledge proofs (ZKP), and fully-homomorphic encryption (FHE). We illustrate how they’ll apply, in composition with differential privateness, to Rya’s analysis setting. The examples embody settings that must deal with multiple database, account for privateness restrictions from Rya, and guarantee correctness even when some events misbehave.
SMPC. With safe multiparty computation (SMPC) (e.g., Yao and GMW protocols), Rya can study a statistic computed over the mixed databases of Alice and Bob, with out truly combining the databases. Alice and Bob don’t see one another’s information, and Rya learns nothing in regards to the databases, apart from what could be inferred from the (differentially non-public) obtained statistic (see Determine 1).
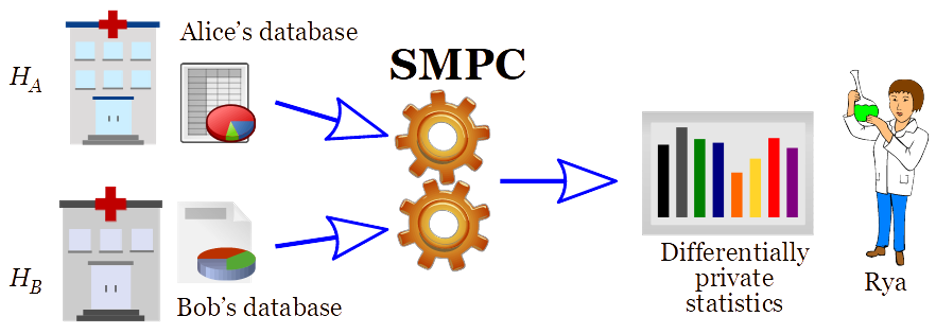
Determine 1: “Safe computation” of differentially non-public statistics from mixed databases
The appliance of SMPC along with differential privateness, as showcased in Determine 1, constitutes a safer various to “central DP” and to “native DP”, the place a curator combines the info but additionally turns into topic to privateness breaches, as defined in a earlier publish. Central DP compromises on safety, by requiring a probably hackable curator to function custodian of the info from a number of hospitals, to have the ability to reply queries in a DP method. Native DP makes a tradeoff between privateness and accuracy, mitigating the foreseeable case of the hacking of the curator, by requiring that the info despatched from every hospital to the curator has been DP-protected. SMPC (of differentially non-public statistics) allows one of the best of each worlds: it gives the best-possible accuracy (as in central DP), and it avoids the leakage potential from the doable breach of a curator (in each central and native DP).
A unique utility of SMPC, to keep away from requiring on-line availability of the unique sources (the hospitals), is to make use of a distributed curator (see Determine 2). Right here, the info from every hospital is secret shared, in order that no sole part of the curator is aware of the info, however a threshold variety of them is enough to reply any question, i.e., utilizing SMPC to compute over the secret-shared information. Presently, the MPC Alliance is a consortium that joins greater than 40 firms and actively engaged in growing and implementing SMPC options.
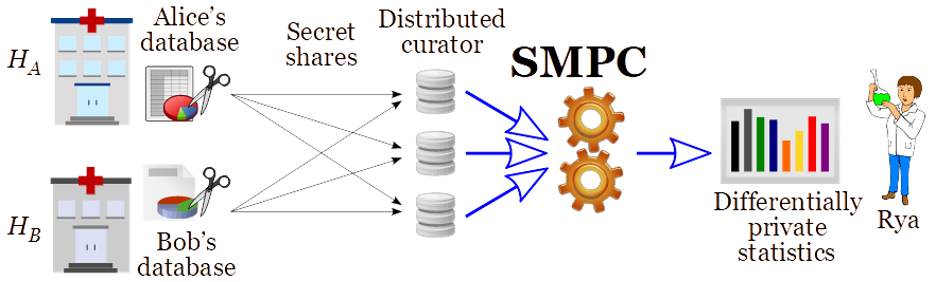
Determine 2: Differential privateness through a distributed curator, utilizing SMPC over secret-shared information
PSI. With private set intersection (PSI) (e.g., Matchmaking and Oblivious Switching protocols), Alice and Bob can decide the set of sufferers which can be frequent throughout their databases, with out sharing any details about different sufferers. Naturally, this intersection could be thought-about delicate data that ought to stay non-public. A variant referred to as PSI cardinality can be utilized to compute statistics in regards to the frequent sufferers, reminiscent of what number of there are, with out divulging the set itself (see Determine 3). The talked about PSI# may also be thought-about per age and per analysis.
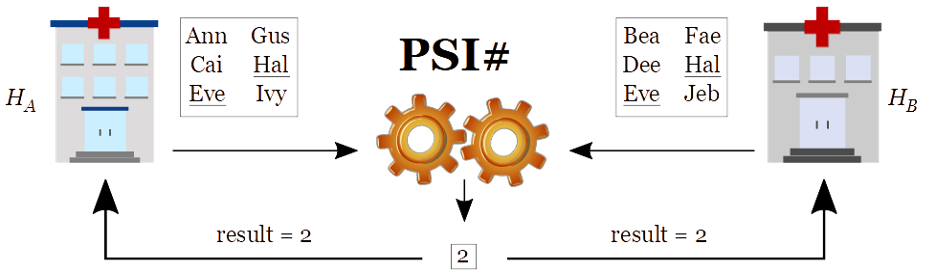
Determine 3: Non-public set intersection cardinality (PSI#) of sufferers throughout two hospitals
We observe that even the cardinality of the intersection could also be delicate data. Subsequently, this multi-party statistic can itself be topic to differential privateness safety. From a distinct angle, the statistic may also be helpful for the hospitals to find out methods to parametrize their differential privateness safety stage for subsequent queries from exterior researchers. This may occasionally enhance privateness and/or accuracy in settings the place Rya will later be individually querying each hospitals. Conceivably, this might be helpful in a setting associated to the COVID-19 pandemic, as thought-about in an utility the place a celebration learns a danger of an infection primarily based on the variety of encountered individuals which have been identified as contaminated.
PIR. With private information retrieval (PIR), Rya is allowed to study the results of a question despatched to Alice’s database, with out Alice studying what was queried (see Determine 4). Recalling our instance from Desk 1, Rya can study the differentially non-public approximation (A’=119.5) of the quantity (A=123) of sufferers in HA, with analysis X and inside the age vary 31–60, with out Alice studying the queried age-range. Naturally, this may be generalized to cover which analysis (X) was queried.
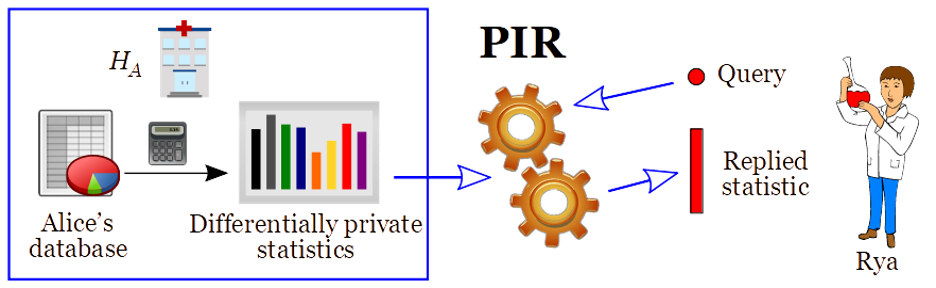
Determine 4: Private information retrieval (PIR) of a differentially non-public statistic
ZKP. Zero-okaynowledge proofs (ZKPs) enable making proofs about information that has one way or the other been “dedicated” (for instance, by disclosing an encrypted model of a database), with out revealing the precise information. Thus, as soon as the info has been dedicated, a database proprietor can show that the reply given to a sure question accurately pertains to information that has not modified. This can be a useful gizmo for permitting accountability whereas defending privateness. Specifically, ZKPs may also be used to allow different PEC strategies (reminiscent of SMPC, PSI and PIR) within the so-called malicious mannequin, the place any of the events (Alice and Bob) may in any other case undetectably deviate from the agreed protocol. For instance, a ZKP can be utilized by Alice to show to Rya that a solution satisfies an applicable differential privateness safety, i.e., ensuing from an accurate noise addition, with respect to the unique secret database (see Determine 5). Presently, zkproof.org is an open initiative that seeks to mainstream the event of interoperable, safe, and sensible ZKP know-how.
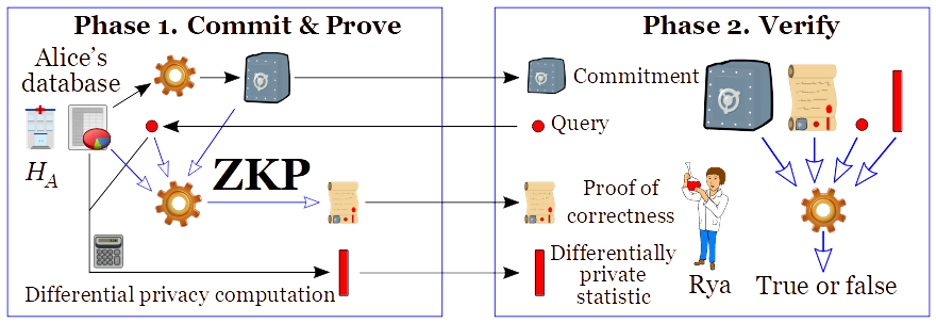
Determine 5: Differentially non-public reply, with a zero-okaynowledge proof (ZKP) of correctness
FHE. Fully-homomorphic encryption (FHE) permits computing over encrypted information, with out figuring out the key key. In different phrases, somebody with out the key key (wanted to decrypt) is ready to remodel a ciphertext (i.e., the encryption of a plaintext) into a brand new ciphertext that encrypts an meant transformation of the plaintext. Conceptually, Rya can encrypt the meant question, ship it to at least one or varied hospitals, after which let the hospitals remodel the encrypted question into an encrypted DP-protected reply, which Rya can later decrypt (see Determine 6). The computation could be made sequentially throughout hospitals, with every new transformation remaining encrypted till the ultimate stage of decryption by Rya.
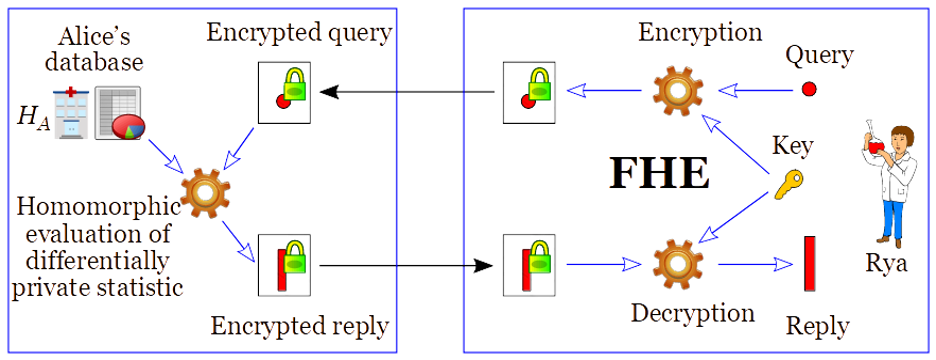
Determine 6: Utilizing FHE for personal computation of differential non-public statistics
FHE is a pure primitive to allow privacy-preserving delegation of computation. The reader might observe that the FHE use-case in Determine 6 is similar to the PIR use-case in Determine 4. Certainly, FHE can be utilized as a primitive for quite a few different privacy-enhancing cryptography instruments, together with PIR, PSI, and SMPC. A typical implementation profit is that it allows options with minimal communication complexity. A doable draw back of FHE is that it may be computationally dearer than different options. Nonetheless, there are purposes for which FHE is sensible, and the sector is quickly enhancing. The homomorphicencryption.org initiative is selling the standardization of FHE.
Conclusion
The roles of privacy-enhancing cryptography (PEC) and differential privateness are considerably totally different, however they’re complementary. Each forms of strategies are relevant to guard privateness whereas enabling the computation of helpful statistics. In conclusion, the toolkit of the privacy-and-security practitioners ought to embody PEC instruments. They supply further utility whereas defending privateness, together with in interactive and multi-party settings that aren’t amenable to be dealt with by standalone differential privateness. For extra PEC particulars and examples, observe the NIST-PEC undertaking. That is an thrilling space of growth.
Coming Up Subsequent
On this publish we mentioned strategies for linking delicate information throughout a number of information homeowners. However how do we all know if the differentially non-public outcomes we get out shall be helpful? To reply this query requires making use of the correct utility metrics, which is the subject of our subsequent publish. Keep tuned!
This publish is a part of a collection on differential privateness. Be taught extra and browse all of the posts revealed thus far on the differential privateness weblog collection web page in NIST’s Privateness Engineering Collaboration House.
[ad_2]
Source link