[ad_1]

Given the rising reliance of organizations on applied sciences over the previous 50 years, a lot of danger disciplines have advanced into full-fledged danger packages. Lately, cybersecurity, provide chain, and privateness danger administration packages have formalized greatest practices. But the fast evolution of those disciplines generally has led to miscommunication and inefficiencies between these danger packages and overarching enterprise danger administration (ERM) portfolio. The years forward will deal with optimizing coordination and communication between all danger packages and ERM.
To be supportive of mission and enterprise aims, every danger program should perceive how they help the ERM portfolio. An ERM context aggregates and normalizes organizations’ dangers into danger registers and insurance policies. This allows authorities and important infrastructure entities to quantify penalties and allocate assets commensurate with enterprise publicity and shareholder/stakeholder worth. As enterprise penalties are quantified in monetary, mission and popularity metrics, much like these attributed to different enterprise dangers, they allow executives and public officers to prudently reallocate assets amongst all their specific competing danger sorts.
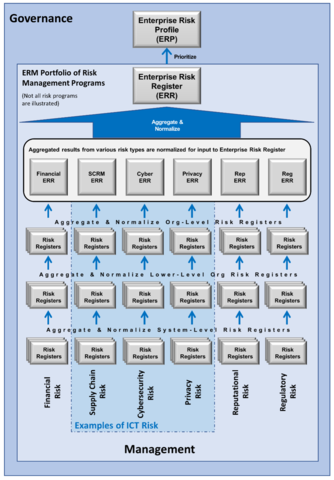
In current years, the NIST Data Know-how Laboratory (ITL) has been publishing steering to codify danger administration greatest practices for particular person packages corresponding to privateness, provide chain, and cybersecurity. In acknowledgement of its expansive constitution and rising applied sciences, ITL is broadening its danger steering to incorporate how all info and communication know-how (ICT) danger packages combine into ERM. This exercise explains how frameworks just like the Cybersecurity Framework, Privateness Framework, synthetic intelligence, info programs and organizations and Cyber Provide Chain Threat Administration will work collectively to help ERM. Every of those ICT frameworks is consultant of a danger program. Dangers inside, throughout, and in-between these packages kind a mosaic of peer and interrelated ICT dangers.
The ICT danger mosaic, which companies and enterprises should navigate, is a posh adaptive system-of-systems composed of hundreds of interdependent elements and a myriad of channels. These embody quite a few digital applied sciences that create, modify, course of, talk and management info in addition to the applying applied sciences. This technique-of-systems offers or assists enterprise or private endeavors and the resultant knowledge represents info, management alerts and sensor readings. As with different advanced systems-of-systems, the interconnectedness of those applied sciences produces system behaviors which can’t be decided by the habits of its particular person elements. That interconnectedness causes dangers that exist between danger packages and throughout a number of danger packages. ITL is continuing with a extra interconnected method to danger frameworks and packages to handle this particular subsect of dangers.
As our programs turn out to be extra advanced, they current exploitable vulnerabilities, emergent dangers, and system instabilities that, as soon as triggered, can have a runaway impact with a number of, extreme, usually irreversible penalties. Within the modern enterprise, emergency and real-time circumstances can flip a comparatively minor ICT-based danger into true Operational Dangers that disrupt a company’s potential to carry out mission or enterprise capabilities. The upcoming ICT danger administration steering will handle a few of these challenges, together with the notion that real-time programs convey real-time dangers and wish real-time resilience.
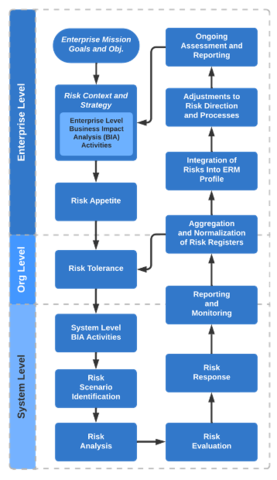
A current NIST Interagency Report pioneers a use case of ERM integration. The NIST IR 8286 Collection of publications demonstrates how you can higher combine cybersecurity with ERM. The Collection helps authorities and important infrastructure entities successfully quantify, finance, and drive their cybersecurity packages commensurate with enterprise publicity, in addition to shareholder and stakeholder worth. The Collection acknowledges the necessity for ongoing bidirectional communication between ERM and danger packages recognizing that the chance disciplines each inform and obtain route from ERM. Particularly, the communication of danger urge for food statements from the ERM portfolio is a means for danger packages to raised determine and monitor dangers utilizing a wide range of associated strategies corresponding to danger tolerance statements, key efficiency indicators, key danger indicators, and controls. Equally, the NISTIR formalizes the usage of danger registers to speak dangers and danger responses between program and portfolio ranges. The sequence highlights business greatest practices for coordination by elevating dangers inside a company for oversight and escalating dangers inside a company for greater stage possession.
Within the upcoming months, NIST will finalize key publications throughout the NIST IR 8286 Collection and publish steering on how you can higher combine ICT danger packages into ERM. These publications will deal with higher communication and coordination throughout danger packages and portfolio. Please proceed offering suggestions on these necessary tips, so we will all take pleasure in a simpler and environment friendly future for danger administration.
[ad_2]
Source link